Phishing attacks are becoming more targeted – and more sophisticated! Criminals are increasingly targeting mobile users by sending malicious content via SMS. What this is all about and how you can best protect yourself – just read on.
Have you ever received one of these SMS messages telling you that a parcel you supposedly ordered could not be delivered and that you should download the service provider’s app via the link contained in the message in order to receive it? But you didn’t order anything… If you didn’t follow the instructions in this message, you did everything right! Because this is so-called smishing, i.e. phishing via SMS. And this scenario described above is just one of many.
Phishing goes mobile
SMS is – despite the numerous messenger services that have been developed in recent years – still a frequently used way to communicate with smartphones. Especially in times of home office and remote work, where private devices are used everyday, a large part of communication takes place via cell phones. It is perceived as secure. Criminals exploit this assumption. The aim of the scammers is to use misleading SMS messages to steal sensitive data and valuable information.
Currently, smishing attacks can be divided into three different categories:
- Malware spreading
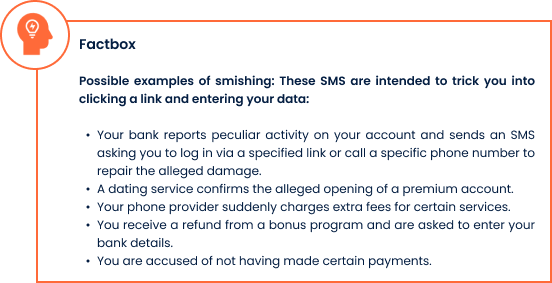
The scenario described above is one of many and is based on classic e-mail phishing. The link in the SMS leads to a website where an app is available for download. This looks confusingly similar to those of parcel delivery companies or other service providers – see the Factbox – but is a fake and contains a banking Trojan. It is activated when the supposed app is downloaded and can access or use all personal data, such as phone numbers, e-mail addresses, and banking data after installation. In addition, the access can result in further malicious SMS being sent to the contacts on the cell phone – a chain reaction with fatal consequences.
The most widespread banking Trojans of this type are currently FluBot and TeaBot. Android devices in particular are affected by this form of attack, as the operating system allows apps from unknown sources to be installed.
- Bank smishing
Login data for online banking is particularly interesting for cybercriminals. Spreading fear is a popular method among hackers to gain access to their victims’ cash deposits: they send SMS messages from the victim’s supposed bank with the information that the bank account has been hacked and provide a phone number or link to prevent further, alleged damage. The phone number often leads directly to the criminals. And the link in the message directs to a fake website. In both cases, the victims are supposed to be tricked into revealing their access data – only to find a looted bank account afterwards. Oftentimes the sender’s number is hidden, so that many victims cannot recognize the source of the text message.
- The grandchild trick as SMS
This type of smishing mainly affects people who are less tech-savvy. In this case, tricksters pose as supposed acquaintances of the victim – the names are often obtained via social media – and hold out the prospect of a financial benefit if a deposit is made in advance to a specific bank account.
How you can best protect yourself and others from smishing
- Don’t click on any of the links and block the sender’s phone number. If you are actually expecting a delivery and are not sure if the SMS is from your package delivery agency, contact them directly. The same goes for your bank account: Log in directly through the browser to get more information.
- Only use apps from reputable sources, i.e. the official app stores or from the provider’s website, to download apps.
- On Android, you can turn off the “Install apps from unknown sources” option in the settings. That way you can protect yourself – and others.
- Report the smishing incident to the consumer advice center. By doing so, you will not only protect yourself, but others as well.
- If such an incident occurs on your work phone, inform members of your organization.
- Raise your awareness of these types of attacks: ask yourself if your bank or parcel service would send you such messages. Would they even have your cell phone number to do so? No bank calls their customers and asks for personal information over the phone. If you receive a call like this, close it immediately.
- Watch out for cryptic links and spelling in body text. In the end, the following always applies: Better safe than sorry….
Already clicked – how to limit damage
- If you suspect that you have been the victim of a smishing attack, set your cell phone to flight mode. This will stop the malicious software from being sent to your contacts.
- Inform your mobile provider about the incident – and your bank, if you have already disclosed your banking details.
- Reset your smartphone to delete all data
Do you have more questions about phishing or you want to learn how you can cyber-secure your business? Our experts at Perseus Technologies will be happy to advise you.
Pic Source: Perseus Technologies GmbH
